Your Data. Your Control. Always.
Run Courdx entirely on-premises with local AI models — no data leaves your network, ever. Or deploy in your private cloud with the same security guarantees.
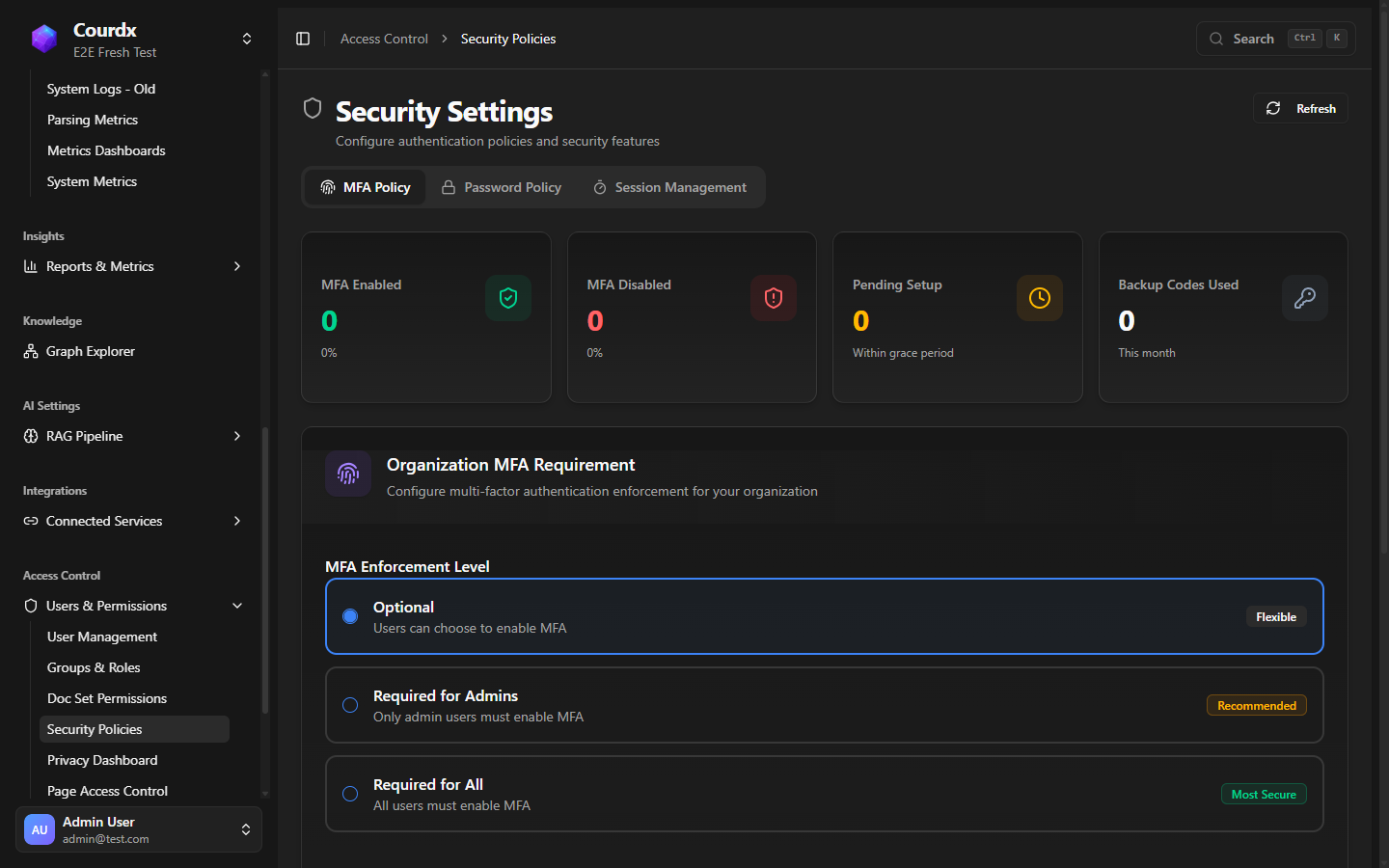
Collection-level permissions, DLP policies, MFA enforcement, PII redaction, prompt injection blocking, and comprehensive audit trails — all built in, not bolted on.
Secure By Design
Every Query. Every Step. Protected.
Security checkpoints at every stage of the pipeline ensure your data stays safe.
Defense in Depth
Multi-Layer Security Architecture
Every layer adds protection. Every access is verified.
5 layers protecting your data
Access Control
Multi-factor authentication & SSO
Data Encryption
End-to-end encryption at rest & transit
Document Security
Prevents data leaks & enforces permissions
Query Guardrails
AI safety & response filtering
Monitoring
Real-time threat detection
Defense-in-Depth Security Architecture
Defense-in-Depth Security Architecture
Deployment
Your Infrastructure. Your Rules.
Choose the deployment model that fits your security requirements.
Cloud SaaS
Fully managed, instant deployment
Best for:
Fast deployment, minimal IT overhead
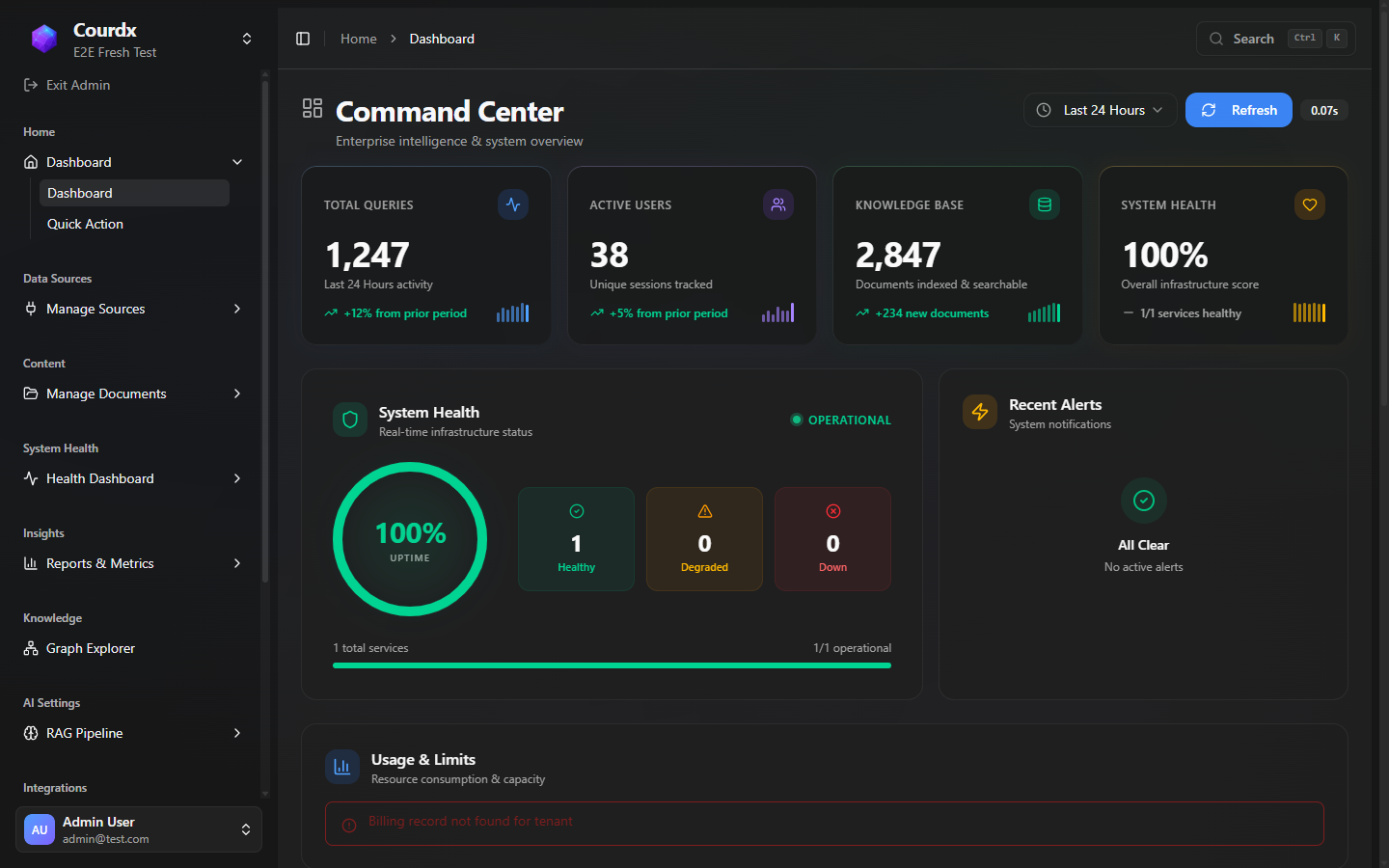
Governance
Enterprise Governance
Define who can create projects, which teams see which data, and whether users can copy or export AI-generated answers. Every policy is configurable per role, team, or project.
Admin Control
- Control WHO can create projects
- Workspace provisioning policies
- Resource quotas per team/user
Data Loss Prevention (DLP)
- Control WHO can copy chat content
- Control WHO can export conversations
- Prevent knowledge from leaving the organization
- Configurable per role, team, or project
Collection-Level Security
- Permissions at the data collection level
- Legal can't see HR data
- Sales can't see Finance data
- Queries automatically filtered by permissions
Users can query and get answers — but cannot extract data outside the organization. This prevents knowledge leakage while maintaining productivity.
AI Safety
AI Safety & Guardrails
Both sides of the conversation are protected. Input guardrails catch prompt injection attempts, PII in queries, and blocked topics before they reach the AI. Output guardrails verify citations, detect hallucinations, and filter toxic or leaked content before it reaches the user.
Input Guardrails
- Prompt injection detection
- PII scrubbing from queries
- Blocked topic enforcement
- Malicious content filtering
Output Guardrails
- Hallucination detection
- PII leak prevention
- Citation verification
- Toxicity filtering
Real Controls
Built-In Security Administration
MFA enforcement, password policies, session management, and role-based access — all from the admin panel.
Compliance
Compliance & Data Protection
AES-256 encryption at rest, TLS 1.3 in transit, multi-tenant row-level security, and comprehensive audit logging. We never train on your data. Built for healthcare, financial services, legal, and government environments.
SOC 2
Compliance ready
GDPR
EU data protection compliance
HIPAA
Healthcare data protection
ISO 27001
Information security management
Security That Meets Your Requirements
Let's discuss your deployment and security needs.